Global “Error524” Smishing Campaign Targeting Multiple Sectors Including Bangladesh
Published on 13-Apr-2026 15:00:00
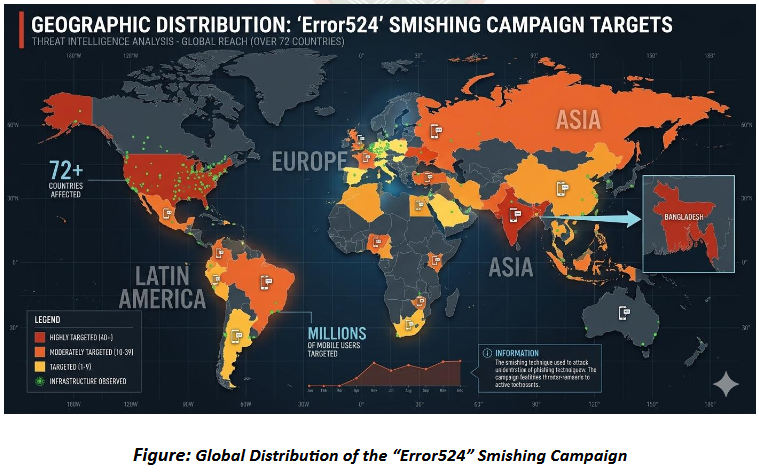
BGD e-GOV CIRT has identified intelligence regarding a large-scale global smishing (SMS phishing) campaign named “Error524” targeting multiple industries including financial services, telecommunications, logistics, retail, and government services.
The campaign uses phishing-as-a-service (PhaaS) infrastructure to distribute SMS messages containing malicious links that redirect victims to phishing websites designed to steal personal information, banking credentials, and payment card data.
Threat intelligence indicates that Bangladesh is among the targeted countries, alongside several regions across Europe, Asia, and the Americas. Due to the impersonation of trusted services and institutions, this campaign poses a significant cybersecurity risk to organizations and citizens in Bangladesh.
Overview of the Threat
The Error524 campaign has been active since late 2025 and continues to evolve using sophisticated phishing infrastructure and evasion techniques.
The campaign impersonates multiple well-known brands and services globally, including:
- Financial institutions
- Government portals
- Telecommunications providers
- Logistics and delivery services
- Retail and loyalty programs
Attackers distribute SMS messages containing shortened URLs, which lead victims to highly realistic phishing websites. The infrastructure supporting the campaign uses cloud hosting, domain rotation, and content filtering techniques to avoid detection
Bangladesh Impact Analysis
Threat intelligence indicates that Bangladesh is included among the targeted countries in the campaign’s victim list. Because the attack methodology relies on impersonating widely used digital services.
These phishing campaigns can affect both organizations and individual users, potentially leading to financial fraud and identity theft.
Attack Methodology
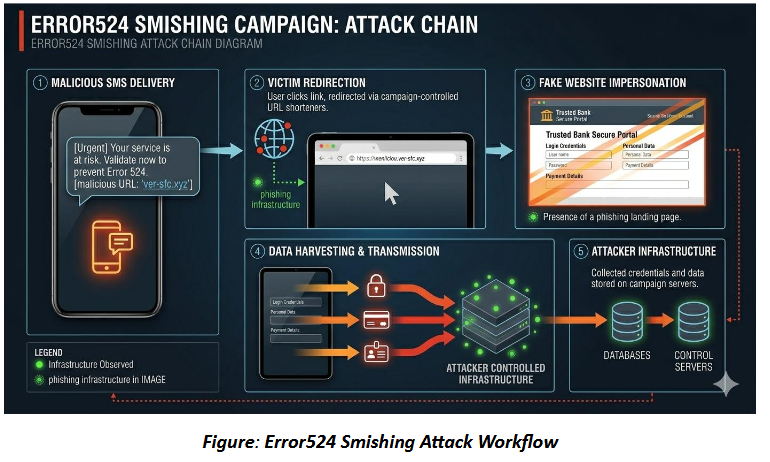
The campaign typically follows a multi-stage attack chain.
Smishing Distribution: Victims receive SMS messages that appear to originate from trusted services. Examples of typical lures include:
- delivery status notifications
- unpaid toll or fine alerts
- account verification requests
- reward or loyalty program offers
These messages contain shortened or disguised malicious links.
Phishing Website Redirection: Clicking the link redirects the victim to a fake website that closely imitates a legitimate service portal. These phishing pages are designed to:
- replicate official branding
- request login credentials
- collect payment information
Data Collection: Victims are prompted to submit sensitive information including:
- personal identification information
- account credentials
- credit or debit card details
- one-time authentication codes
Data Exfiltration: Captured information is transmitted to attacker servers through:
- encrypted WebSocket communication channels
- HTTP POST requests
- centralized phishing backend systems