Cyber Security Alert During Long Holiday
Published on 15-Mar-2026 12:00:00
During extended holiday periods such as Eid-ul-Fitr, cyber threat actors often attempt to exploit reduced operational staffing, delayed incident response, and unattended systems.
Recent cyber threat intelligence analysis indicates the presence of interconnected malware families, botnet infrastructure, and advanced threat actors capable of targeting financial systems, government infrastructure, telecom networks, and internet-facing services.
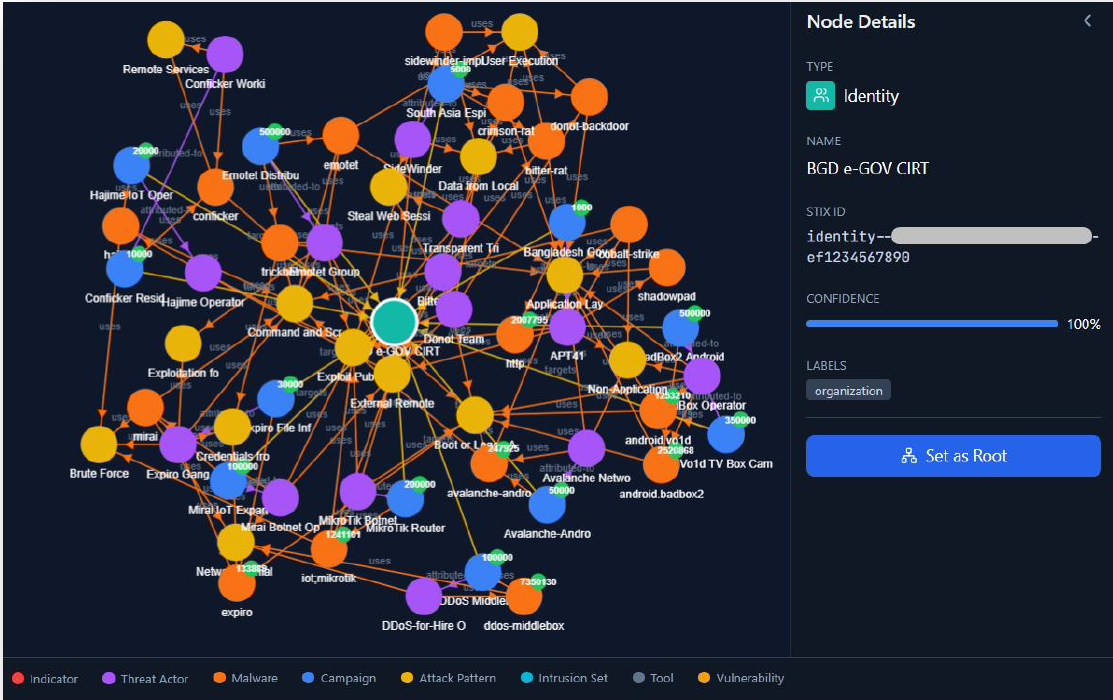
Fig: Relationship graph of threat entities propagating Bangladeshi Organizations
Potential risks during the holiday period include:
- Phishing and credential harvesting campaigns
- Malware infections leading to ransomware attacks
- Botnet-driven Distributed Denial-of-Service (DDoS) attacks
- Exploitation of unpatched internet-facing services
- Unauthorized access through compromised credentials
Organizations operating Critical Information Infrastructure (CII) and essential services in Bangladesh are advised to maintain heightened cybersecurity vigilance and implement preventive security controls during the EID holiday period.
Threat Graph Interpretation
Threat analysis identified several major cyber threat clusters relevant to Bangladesh’s digital ecosystem.
| Cluster | Description |
| Botnet Ecosystem | Mirai, MikroTik Botnet, Avalanche Network, Hajime |
| Banking Malware | Emotet, Trickbot, credential harvesting infrastructure |
| Android Malware / Mobile Botnets | Android BadBox, Android Void, Android Hummer |
| RAT / Backdoor Malware/ Espionage | ShadowPad, Cobalt Strike, Bootkit / Boot or Logon persistence, Crimson RAT, Oblique RAT |
| APT Infrastructure | Lazarus, MuddyWater, Bitter APT, Expiro Gang |
| Threat Actor Operations | SideWinder, Transparent Tribe, Donot Team, Patchwork |
| Command & Control Infrastructure | C2 servers, malicious IP infrastructure |
| Target Infrastructure | Routers, IoT devices, application servers, application layer services |
These clusters demonstrate a multi-stage attack capability, where attackers may combine phishing, malware loaders, remote access tools, and botnet infrastructure to compromise networks.
Potential Threat Scenarios During Holiday
Phishing and Email Attacks: Successful phishing attempts may result in credential theft or malware infection. Attackers may distribute phishing emails disguised as:
- Holiday greetings
- Financial notifications
- Government announcements
- HR or payroll update
Malware & Ransomware Deployment: Cybercriminal groups may deploy malware to establish persistence within networks and later launch ransomware attacks or data exfiltration operations.
Typical attack chain:
Phishing Email → Malware Loader → Remote Access → Lateral Movement → Ransomware Deployment
Botnet-based DDoS Attacks: IoT and router-based botnets may launch Distributed Denial-of-Service (DDoS) attacks targeting:
- Government portals
- Online banking systems
- Payment gateways
- Telecom services
Exploitation of Unpatched Systems: Successful exploitation may lead to unauthorized access or full system compromise. Threat actors may scan for vulnerable services such as:
- VPN gateways
- Web servers
- Remote desktop services
- Misconfigured cloud infrastructure
Recommended Preventive Measures
Organizations are advised to implement the following measures before the holiday period:
- Maintain round-the-clock monitoring of systems, networks, and user activities through Security Operations Centers (SOC) or designated monitoring teams.
- Deploy and regularly update advanced security solutions such as Security Information and Event Management (SIEM), Web Application Firewall (WAF), and endpoint protection platforms to detect and mitigate cyber threats.
- Restrict remote access to systems through secure encrypted VPN connections with Multi-Factor Authentication (MFA) enabled.
- Block or restrict traffic originating from untrusted or suspicious networks where operationally feasible.
- Ensure all operating systems, applications, and servers are updated with the latest security patches, and phase out unsupported or end-of-life software.
- Maintain secure and redundant backups of critical data and periodically test restoration procedures to ensure business continuity in case of cyber incidents.
- Temporarily restrict non-essential system access, and review or disable unused, dormant, or inactive user accounts.
- Strengthen monitoring of internet-facing systems such as web servers, VPN gateways, email infrastructure, and remote access services.
- Immediately report any Indicators of Compromise (IOCs), suspicious activity, or cyber incidents to BGD e-GOV CIRT at: cti@cirt.gov.bd, info@cirt.gov.bd
Organizations operating critical digital infrastructure are strongly encouraged to maintain heightened cyber security awareness and operational readiness during the Eid holiday period.
Proactive monitoring, timely patching, and rapid incident response will significantly reduce the risk of cyber incidents affecting national digital services.