Lately we have been seeing a new variant of Android banking malware which is well-developed and provides numerous unique features such as a ransomware module. Based on the BTC addresses that are used in the source code it seems that the actors behind this new Android malware are successful cybercriminals with over 1.5 million dollars in BTC. It is very unlikely that the actors behind...
Read More
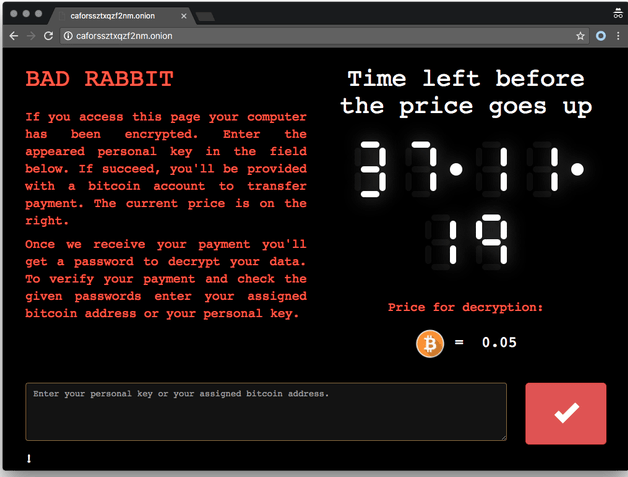
ব্যাড র্যাবিট (Bad Rabbit) র্যানসমওয়্যার কি : সাইবার নিরাপত্তা গবেষকরা সম্প্রতি ‘ব্যাড র্যাবিট’ নামে নতুন একটি র্যানসমওয়্যার শনাক্ত করেছেন, যা এরই মধ্যে ইস্টার্ন ইউরোপীয় দেশগুলির সরকারী-বেসরকারী সংস্থা, ব্যবসা প্রতিষ্ঠান এই র্যানসমওয়্যার দ্বারা আক্রান্ত হয়েছে বলে জানা গিয়েছে। ‘ওয়ানাক্রাই’ WannaCry ও ‘পেটয়্যা’ Petya র্যানসমওয়্যার দুটির সাথে মিল রয়েছে এই নতুন ব্যাড র্যাবিট (Bad Rabbit) র্যানসমওয়্যার এর । এখন পর্যন্ত প্রাপ্ত তথ্য মতে জানা যায় যে, এই...
Read More
After last week we had the KRACK and ROCA cryptographic attacks, this week has gotten off to a similarly “great” start with the publication of a new crypto attack known as DUHK (Don’t Use Hard-coded Keys). The issue at the heart of the DUHK attack is a combination of two main factors. The first is the usage of the ANSI X9.31 Random Number Generator (RNG). This is an algorithm...
Read More
Security researchers have spotted a new Android banking trojan named LokiBot that turns into ransomware and locks users’ phones when they try to remove its admin privileges. The malware is more banking trojan than ransomware — according to SfyLabs researchers, the ones who discovered it — and is used for this purpose primarily. Just like similar Android banking trojans, LokiBot works by showing fake login...
Read More
The Pirate Bay, the world’s largest BitTorrent indexer, is a massive online source for digital content– movies, games and software—and is among the top 100 most popular websites globally, according to Alexa. No stranger to controversy for its role in illegal downloads, a few weeks ago it was discovered that The Pirate Bay operators have begun using the website users’ computer resources to mine the Monero...
Read More
Description: The error page mechanism of the Java Servlet Specification requires that, when an error occurs and an error page is configured for the error that occurred, the original request and response are forwarded to the error page. This means that the request is presented to the error page with the original HTTP method. If the error page is a static file, expected behaviour is...
Read More
Description: Race condition in the (1) CREATE INDEX and (2) unspecified ALTER TABLE commands in PostgreSQL before 8.4.20, 9.0.x before 9.0.16, 9.1.x before 9.1.12, 9.2.x before 9.2.7, and 9.3.x before 9.3.3 allows remote authenticated users to create an unauthorized index or read portions of unauthorized tables by creating or deleting a table with the same name during the timing window. Impact: Successful exploits may allow...
Read More
Description: Race condition in the ALSA subsystem in the Linux kernel before 4.13.8 allows local users to cause a denial of service (use-after-free) or possibly have unspecified other impact via crafted /dev/snd/seq ioctl calls, related to sound/core/seq/seq_clientmgr.c and sound/core/seq/seq_ports.c. Impact: An attacker can exploit this issue to cause a local denial-of-service condition; other attacks may also be possible. Mitigation: Administrators may disable administrative privileges on...
Read More
Almost the complete Master File Table (MFT) can be decrypted. In this post, we describe our approach to collect more keystream bytes, which eventually leads to decrypt the complete disk. Technical Analysis Encryption of Files MFT records already store the content of a file, if the file is at most 900 bytes in size. This means that the tool decryptPetya.py from our first blog post can already...
Read More
The Anti-Phishing Working Group’s latest report found upticks in phishing attacks against companies in the Logistics & Shipping as well Cloud Storage & File Hosting sectors, mounted by cyber gangs against the accounts of both individuals and enterprises. Once they steal usernames and passwords, the criminals can then steal not only funds, but also use services to spend spam mail, order goods for resale, and other...
Read More