Multiple Vulnerabilities in SonicWall SMA 100 Series Could Allow for Arbitrary Code Execution
by CIRT Team
DESCRIPTION:
Multiple vulnerabilities in SonicWall SMA 100 Series could allow for
arbitrary code execution. Successful exploitation of these
vulnerabilities could allow for arbitrary code execution. The SonicWall
SMA 100 Series is a unified secure access gateway that enables
organizations to provide access to any application, anytime, from
anywhere and any devices, including managed and unmanaged. Depending on
the privileges associated with the application, an attacker could then
install programs; view, change, or delete data; or create new accounts
with full user rights. Applications that are configured to have fewer
user rights on the system could be less impacted than those that operate
with administrative user rights.
IMPACT:
Multiple vulnerabilities in SonicWall SMA 100 Series could allow for
arbitrary code execution. Details of these vulnerabilities are as follows:
* A Unauthenticated Stack-based Buffer Overflow which could allow for an
attacker to potentially execute code as a ‘nobody’ user in the
appliance. (CVE-2021-20038)
* An Authenticated Command Injection Vulnerability as Root which could
allow for an attacker to potentially execute code as a ‘nobody’ user in
the appliance. (CVE-2021-20039)
* An Unauthenticated File Upload Path Traversal Vulnerability which could
allow a remote unauthenticated attacker to upload crafted web pages or
files as a ‘nobody’ user. (CVE-2021-20040)
* An Unauthenticated CPU Exhaustion Vulnerability which could result in
DoS. (CVE-2021-20041)
* A Unauthenticated “Confused Deputy” Vulnerability which could allow an
unauthenticated attacker to bypass firewall rules. (CVE-2021-20042)
* A getBookmarks Heap-based Buffer Overflow which could allow for an
attacker to potentially execute code as a ‘nobody’ user in the
appliance. (CVE-2021-20043)
* A Post-Authentication Remote Code Execution (RCE) which could allow a
remote authenticated attacker to execute OS system commands in the
appliance. (CVE-2021-20044)
* Multiple Unauthenticated File Explorer Heap-based and Stack-based
Buffer Overflows which could allow for an attacker to potentially
execute code as a ‘nobody’ user in the appliance. (CVE-2021-20045)
Successful exploitation of these vulnerabilities could allow for
arbitrary code execution. Depending on the privileges associated with
the application, an attacker could then install programs; view, change,
or delete data; or create new accounts with full user rights.
Applications that are configured to have fewer user rights on the system
could be less impacted than those that operate with administrative user
rights.
SYSTEM AFFECTED:
* SonicWall SMA 100 Series 10.2.1.0-17sv and earlier
* SonicWall SMA 100 Series 10.2.1.1-19sv and earlier
* SonicWall SMA 100 Series 10.2.1.2-24sv and earlier
* SonicWall SMA 100 Series 9.0.0.11-31sv and earlier
* SonicWall SMA 100 Series 10.2.0.8-37sv and earlier
RECOMMENDATIONS:
We recommend the following actions be taken:
* Apply appropriate patches provided by SonicWall to vulnerable systems
immediately after appropriate testing.
* Block external access at the network boundary, unless external parties
require service.
* If global access isn’t needed, filter access to the affected computer
at the network boundary. Restricting access to only trusted computers
and networks might greatly reduce the likelihood of successful exploits.
* Run all software as a nonprivileged user with minimal access rights.
To mitigate the impact of a successful exploit, run the affected
application as a user with minimal access rights.
* Deploy network intrusion detection systems to monitor network traffic
for malicious activity.
* Deploy NIDS to detect and block attacks and anomalous activity such as
requests containing suspicious URI sequences. Since the webserver may
log such requests, review its logs regularly.
* Implement multiple redundant layers of security. Since this issue may
be leveraged to execute code, we recommend memory-protection schemes,
such as nonexecutable stack/heap configurations and randomly mapped
memory segments. This tactic may complicate exploit attempts of
memory-corruption vulnerabilities.
REFERENCES:
https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-20038
https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-20039
https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-20040
https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-20041
https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-20042
https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-20043
https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-20044
https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-20045
https://www.sonicwall.com/support/product-notification/product-security-notice-sma-100-series-vulnerability-patches-q4-2021/211201154715443/
Published: 4 January 2022, 12:29:30 BST
Recommended Posts
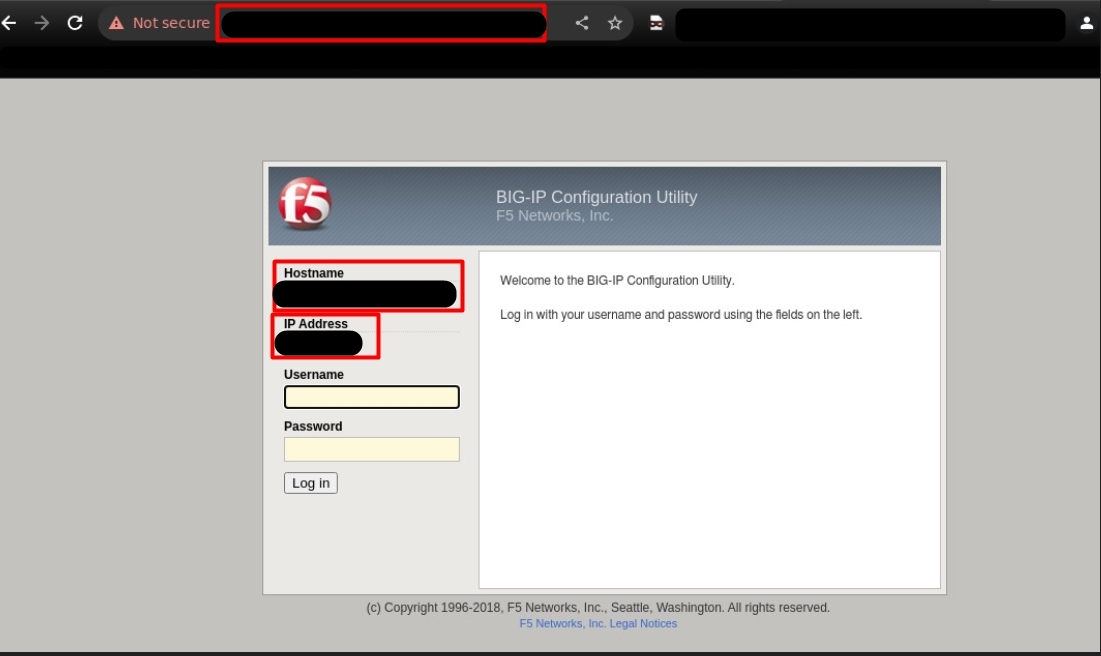
Active Exploitation of Critical F5 BIG – IP Vulnerability (CVE–2023-46747) Uncovered in Bangladesh
06 Nov 2024 - Security Advisories & Alerts










